About Us
Jadab Technologies Limited is an innovative, leading–edge technology company providing cutting–edge cyber security solutions to our customers. We specialize in providing advanced security solutions for the public and private sectors around the world. At Jadab Technologies Limited, we are passionate about helping our customers protect their most valuable assets – their data. We understand the importance of data security and the need to keep it safe from theft, vandalism, and cyber–attacks. That’s why we provide the most advanced, reliable and secure cyber security solutions available. Our team of highly trained and experienced cyber security experts is dedicated to staying ahead of the curve and providing our customers with the best possible solutions. We work closely with our customers to design, develop and implement the best cyber security solutions to meet their individual needs. We believe in creating long–term relationships with our customers and providing them with the highest quality service. We are constantly looking for ways to improve our services and ensure our customers are receiving the best experience possible. We are proud to provide our customers with the best cyber security solutions from the top companies in the industry, such as Rapid7, Sophos,Cyberark and many more solutions. Our experienced team of experts can help you choose the best security solution for your organization, so you can feel confident that your data is safe and secure.
Information Gathering
We conduct reconnaissance using open-source intelligence (OSINT) techniques to identify sensitive design and configuration information of the application, systems, and organisation that is exposed both directly (on the organisation’s website) or indirectly (on a third party website).
Application Security
Enhancing security procedures during the software development lifecycle and throughout the application lifecycle is one of the security measures. All app sec procedures should reduce the possibility that bad actors would be able to access systems, applications, or data without authorisation. Application security’s overarching purpose is to stop attackers from accessing, altering, or deleting confidential or proprietary data.
A countermeasure or security control is any step taken to guarantee application security. A security control is described as “”a safeguard or countermeasure prescribed for an information system or an organisation designed to protect the confidentiality, integrity, and availability of its information and to meet a set of defined security requirements” by the National Institute of Standards and Technology (NIST).
Cyber Risk Audit
A Cyber Risk Audit assesses the potential implications, risks and costs of a data breach or cyber attack on the organisation and its stakeholders.
A Cyber Risk Audit is essential in the Cyber Resilience Planning lifecycle. Cyber risk auditing allows organisations to establish their current cyber security posture, identify risks, and control gaps. Through a tailored programme of questions, which ensures that the appropriate level of detail is reached, a cyber risk audit enables organisations to put in place measures that will reduce cyber security risk and achieve compliance with legal obligations.
A cyber risk audit is a process designed to thoroughly assess, verify and validate how well an organisation understands, manages and controls its cybersecurity risks. The risk assessment process can help an organisation identify the likelihood of an incident occurring and its potential impacts on the company’s operations, assets and reputation. Using the information from a cyber risk audit, companies can develop strategies to manage their cyber vulnerabilities effectively.
Business Email Compromise (BEC)
BEC attacks are particularly difficult to prevent. This is due to the fact that perpertrators rely on social engineering techniques and impersonation to deive people into acting on the attackers behald, as opposed to employing malware. Threat detection solutions used traditionally to combat BEC attacks that analyse metadata, links and email headers often miss these attack strategies.
BEC attacks do not require advanced tools or tradecraft to execute. As such, they are present in any forms, with the level of sophistication driven by the attacker’s ability and motivation. Attackers will research their target and setup a spoof domain (or compromise a legitimate email) to send a falsified financial email to their target. This can be difficult to detect, with attackers constantly developing more advanced fraud techniques.We are here for your needs.
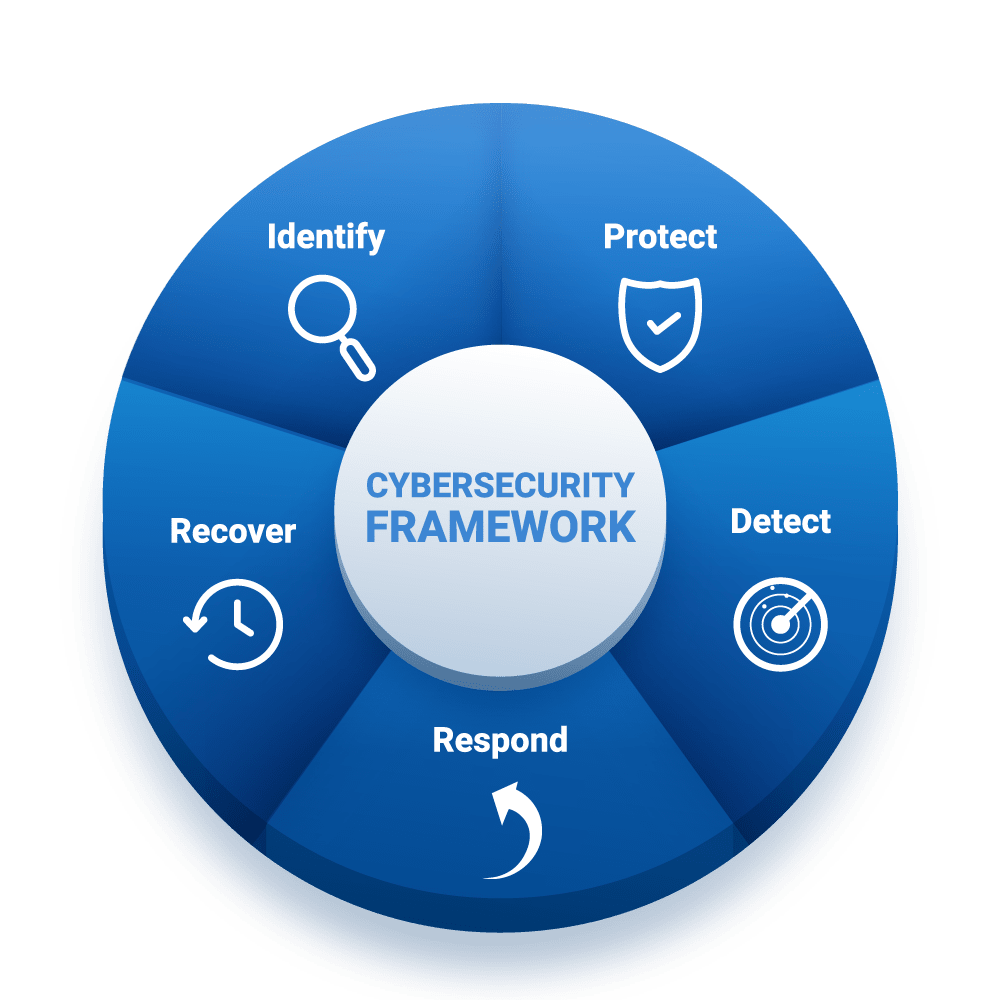
Approach
Our Approach to Security & Prevention
At Jadab Technologies, we understand the importance of security and prevention when it comes to protecting your business and its data. That’s why we strive to provide the most comprehensive, cutting–edge security solutions available today. Our approach to security and prevention begins with a comprehensive evaluation of your existing security infrastructure. We start by understanding your business and its specific needs, as well as the threats that your organization is facing. We then work with you to create a customized security solution that meets your unique requirements. We also offer a range of training and awareness services to ensure that your staff are up-to-date with the latest cyber security threats and best practices. Our team of experts can provide custom training sessions to your employees, designed to ensure that they understand the importance of security and how to protect your data. Finally, we offer ongoing support and maintenance services to ensure that your security system remains up-to-date and effective. We can provide regular system updates to ensure that your security systems are always running at optimal levels, as well as troubleshooting and repairs if needed. At Jadab Technologies, we understand that security and prevention are the keys to keeping your business safe. That’s why we strive to provide our customers with the most comprehensive security solutions available today. Our team of experts is here to help you create a customized security solution and to provide ongoing support and maintenance. Contact us today to find out how we can help protect your business.